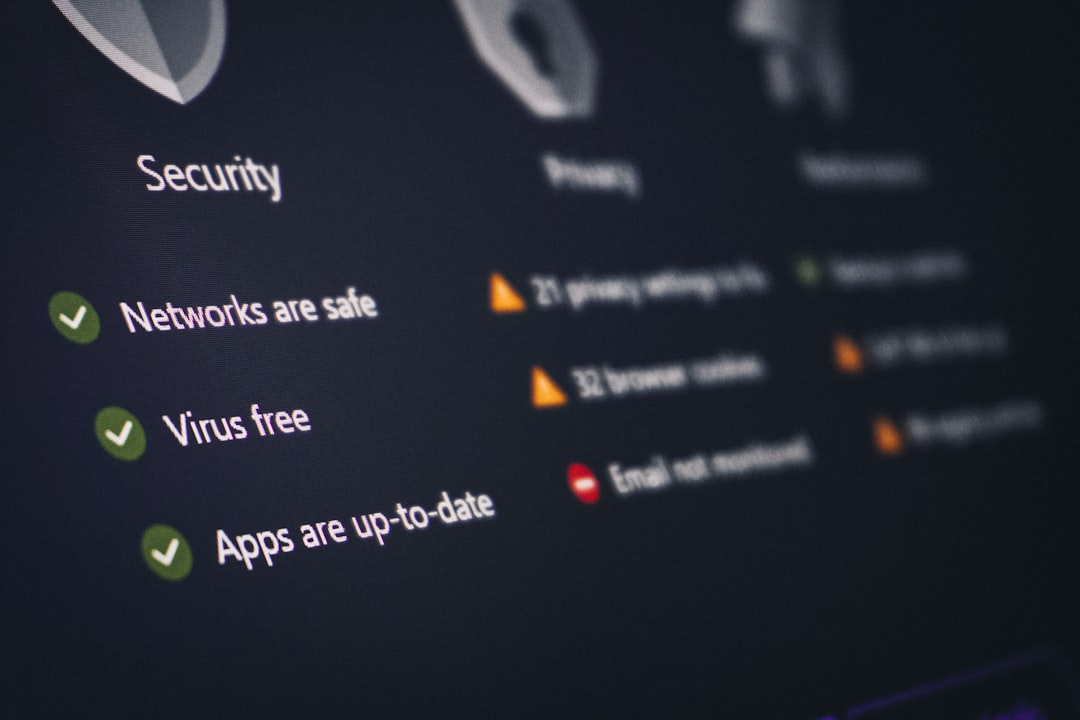
OpenClaw, an open-source AI agent that security firms warn is “insecure by default,” has integrated VirusTotal’s malware scanning into its ClawHub skills marketplace following weeks in which security researchers documented malicious extensions and unauthorized deployments within enterprises. The integration allows automatic scanning of all skills before they are made available for download, marking them as benign, suspicious, or malicious, with immediate blocking of harmful skills.
What This Means
This development highlights increasing vulnerabilities in AI-driven platforms, where the attack surface grows significantly as more skills and extensions are published — attracting malicious actors who exploit these ecosystems to reach enterprise environments. Organizations that have deployed OpenClaw or similar AI agent frameworks without proper vetting may already have malicious extensions operating within their environments. The reactive nature of this security update — implemented after researchers documented active exploitation — is a pattern common to rapidly growing open-source platforms and should inform how your organization evaluates AI tooling.
What To Do Next
- Audit existing deployments: Verify whether OpenClaw or similar AI agents are deployed in your environment, including shadow IT installations not sanctioned by your security team.
- Block unauthorized skills: Review and remove any skills marked as suspicious or malicious in ClawHub, and block unauthorized deployments of OpenClaw organization-wide.
- Implement monitoring: Establish policies for regular monitoring of published skills in AI marketplaces, ensuring security teams review flagged items before they reach production environments.
- Develop AI governance policy: Establish a clear policy governing which AI tools and extensions are approved for organizational use, with a defined review and approval process for new additions.
- Prepare an AI-specific incident response plan: Develop response procedures specifically for AI-driven applications, detailing steps for addressing unauthorized deployments and malware incidents.